Cybersecurity Tools for Small Businesses: In today’s digital age, small businesses face a growing threat of cyberattacks. The importance of cybersecurity cannot be emphasized enough, as data breaches and cyber threats can lead to significant financial losses and damage to a company’s reputation. To ensure the safety and security of sensitive information, small businesses must invest in reliable cybersecurity tools.
Table of Contents
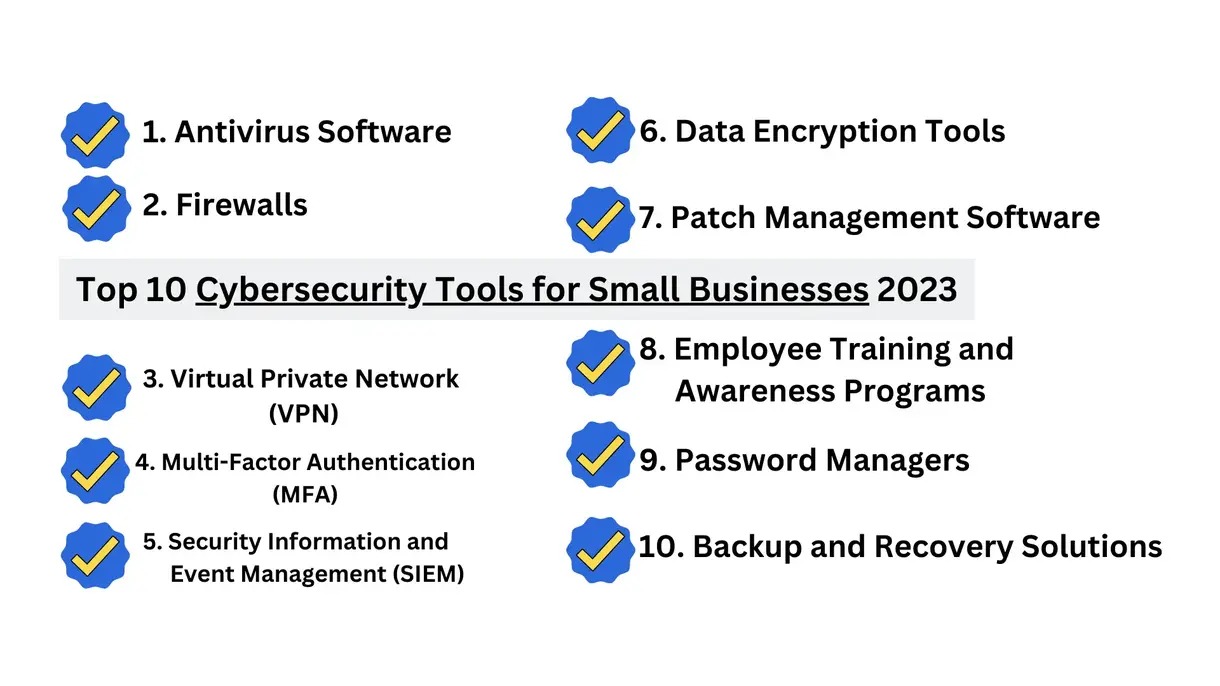
In this article, we will explore the top cybersecurity tools that can help small businesses protect their valuable data.
1. Antivirus Software
1.1. What is Antivirus Software?
- Scans and detects malware and viruses.
- Provides real-time protection.
- Regularly updates to stay ahead of emerging threats.
An antivirus software is the first line of defense against malware and viruses. It scans and detects malicious software, preventing them from infecting your computer systems. Look for reputable antivirus solutions that offer real-time protection and regular updates to stay ahead of emerging threats.
1.2. Free Antivirus Software
1.2.1. Avast Free Antivirus
Features of Avast Free Antivirus
| Features | Description |
| Real-Time Protection | Provides continuous monitoring and real-time scanning to detect and block malware, viruses, and other threats. |
| CyberCapture | Automatically sends suspicious files to the Avast Threat Labs for analysis, ensuring rapid response to emerging threats. |
| Wi-Fi Inspector | Scans your network for vulnerabilities and helps you secure your Wi-Fi connection. |
Benefits of Avast Free Antivirus
| Benefits | Description |
| Strong Protection | Avast’s real-time protection and threat detection keep your devices safe from various cyber threats. |
| Fast Response | CyberCapture ensures that new and unknown threats are quickly analyzed and addressed. |
| Wi-Fi Security | The Wi-Fi Inspector helps you identify and fix potential security issues with your wireless network. |
1.2.2. AVG Antivirus Free
Features of AVG Antivirus Free
| Features | Description |
| Core Antivirus Functionality | Provides essential protection against viruses, malware, and spyware. |
| Email and Link Scanning | Scans emails and web links to detect and block potential threats. |
| Automatic Updates | Regularly updates its virus database to keep your system protected from the latest threats. |
Benefits of AVG Antivirus Free
| Benefits | Description |
| Simple and Effective | AVG offers straightforward antivirus protection without consuming excessive system resources. |
| Email Safety | The email and link scanning feature helps prevent phishing attempts and dangerous downloads. |
| Up-to-Date Protection | Automatic updates ensure your antivirus is equipped to detect and remove the latest threats. |
1.2.3. Avira Free Antivirus
Features of Avira Free Antivirus
| Features | Description |
| Advanced Detection | Uses powerful scanning algorithms to identify and neutralize malware, ransomware, and other threats. |
| Real-Time Protection | Constantly monitors your system for suspicious activities and provides real-time threat blocking. |
| Privacy Tools | Includes a free VPN service and a browser extension to enhance online privacy and security. |
Benefits of Avira Free Antivirus
| Benefits | Description |
| High Detection Rate | Avira’s advanced scanning engine ensures effective threat detection and removal. |
| Continuous Monitoring | The real-time protection feature keeps your devices safe from malware in real-time. |
| Enhanced Privacy | Avira’s VPN and browser extension help protect your online activities and personal data. |
All three free antivirus tools – Avast Free Antivirus, AVG Antivirus Free, and Avira Free Antivirus – offer essential protection against common cyber threats. Their real-time scanning, regular updates, and additional security features make them valuable choices for users seeking reliable, free antivirus solutions. These antivirus programs help keep your devices and data safe from malicious software and ensure a safer and more secure online experience.
2. Firewalls
- Acts as a protective barrier for your internal network.
- Monitors incoming and outgoing traffic.
- Blocks unauthorized access and potential cyber threats.
Firewalls act as a barrier between your internal network and the outside world. They monitor incoming and outgoing traffic, blocking unauthorized access and potential cyber threats. Firewalls can be implemented at both hardware and software levels to provide added security layers.
Free Tools:
ZoneAlarm Free Firewall
Features of ZoneAlarm Free Firewall
| Features | Description |
| Two-Way Firewall | Monitors both inbound and outbound traffic, providing comprehensive protection for your network. |
| Application Control | Allows users to manage which applications can access the internet, preventing unauthorized connections. |
| Identity Theft Protection | Includes advanced security measures to safeguard personal information and prevent identity theft. |
| Wi-Fi Network Security | Scans and protects your wireless network from potential threats and intruders. |
Benefits of ZoneAlarm Free Firewall
| Benefits | Description |
| Robust Protection | ZoneAlarm acts as a strong barrier, blocking unauthorized access and potential cyberattacks. |
| User-Friendly Interface | The firewall’s intuitive interface makes it easy to configure and use for both novice and experienced users. |
| Real-Time Threat Detection | Provides continuous monitoring and real-time alerts for suspicious activities on your network. |
| Identity Protection | The firewall’s identity theft protection features help keep personal information safe from prying eyes. |
Comodo Firewall
Features of Comodo Firewall
| Features | Description |
| Default Deny Approach | Blocks all unknown applications from accessing the internet until the user approves them, enhancing security. |
| Auto-Sandboxing | Suspicious or unrecognized files are executed in an isolated virtual environment, preventing potential harm to the system. |
| Host Intrusion Prevention System (HIPS) | Monitors system activities and behaviors, detecting and blocking suspicious actions. |
| Secure Shopping | Offers a secure browsing environment for online shopping and banking activities. |
Benefits of Comodo Firewall
| Benefits | Description |
| Enhanced Security | Comodo’s default deny approach ensures that only trusted applications have internet access, minimizing the risk of malware infiltration. |
| Advanced Threat Detection | Auto-sandboxing and HIPS add an extra layer of protection, identifying and neutralizing potential threats. |
| Customizable Security Rules | Users can customize firewall settings to fit their specific security needs and preferences. |
| Safe Online Transactions | Comodo’s secure shopping feature protects sensitive financial activities from potential keyloggers and threats. |
Sophos XG Firewall Home Edition
Features of Sophos XG Firewall Home Edition
| Features | Description |
| Enterprise-Grade Firewall | Offers powerful firewall capabilities typically seen in enterprise-level solutions. |
| Web Filtering | Includes web filtering features to block access to malicious websites and control users’ web access. |
| Intrusion Prevention System (IPS) | Actively inspects network traffic to identify and prevent cyberattacks and intrusion attempts. |
| SSL VPN | Allows secure remote access to your home network. |
Benefits of Sophos XG Firewall Home Edition
All three firewall solutions – ZoneAlarm Free Firewall, Comodo Firewall, and Sophos XG Firewall Home Edition – offer essential protection for your network and devices. They help block unauthorized access, monitor network traffic, and protect against various cyber threats, ensuring a safer and more secure online experience. Their diverse features and capabilities make them valuable tools in the defense against potential cyber risks.
3. Virtual Private Network (VPN)
- Encrypts internet connections for secure data transmission.
- Ensures data protection when accessing sensitive information remotely.
A VPN encrypts internet connections, ensuring secure data transmission between your devices and the internet. This tool is especially crucial when employees access sensitive information remotely. With a VPN, data remains encrypted and protected from prying eyes.
Free Tools:
Windscribe VPN
Features of Windscribe VPN
| Features | Description |
| Secure Encryption | Windscribe uses strong encryption to protect your internet connection and data from potential eavesdroppers. |
| Multiple Server Locations | Offers servers in various countries, allowing users to access geo-restricted content and enjoy a faster browsing experience. |
| Firewall (Kill Switch) | Includes a built-in firewall that blocks internet access if the VPN connection drops, preventing data leaks. |
| Ad and Tracker Blocking | Blocks ads and trackers to enhance privacy and browsing speed. |
| Split Tunneling | Allows users to route specific traffic through the VPN while keeping other traffic on the regular network. |
Benefits of Windscribe VPN
| Benefits | Description |
| Enhanced Privacy | Windscribe VPN ensures that your online activities are encrypted and protected from prying eyes and potential hackers. |
| Access to Restricted Content | With servers in multiple locations, users can access geo-blocked content and bypass internet censorship. |
| Prevents Data Leaks | The built-in firewall acts as a kill switch, safeguarding your data in case of unexpected VPN disconnections. |
| Improved Browsing Experience | Ad and tracker blocking speeds up your browsing and protects against intrusive advertising. |
ProtonVPN Free
Features of ProtonVPN Free
| Features | Description |
| Strong Encryption | ProtonVPN uses high-end encryption to secure your internet traffic and data. |
| No Data Logging | ProtonVPN has a strict no-logs policy, ensuring that your online activities are not monitored or stored. |
| Swiss-Based | The service is based in Switzerland, known for its strong privacy laws and data protection. |
| Secure Core Servers | Offers Secure Core servers that route traffic through multiple countries for an added layer of security. |
Benefits of ProtonVPN Free
| Benefits | Description |
| Top-Notch Privacy | ProtonVPN’s no-logs policy and Swiss jurisdiction ensure that your online activities remain private and anonymous. |
| Enhanced Security | The use of strong encryption and Secure Core servers provides robust protection against cyber threats. |
| Trusted Service | Being based in Switzerland, ProtonVPN is subject to strict data protection regulations, earning user trust. TunnelBear Free VPN: |
TunnelBear Free VPN
Features of TunnelBear Free VPN
| Features | Description |
| Simple Interface | TunnelBear offers an easy-to-use interface, making it accessible for even non-technical users. |
| GhostBear | A feature that helps bypass VPN blocking, allowing users to access restricted content in restrictive regions. |
| VigilantBear (Kill Switch) | Automatically blocks internet access if the VPN connection drops to prevent data leaks. |
| Limited Data | The free version offers a limited amount of data usage each month. |
Benefits of TunnelBear Free VPN
| Benefits | Description |
| User-Friendly | TunnelBear’s user-friendly interface ensures that anyone can use the VPN without technical knowledge. |
| Access to Restricted Content | GhostBear helps bypass VPN blocking, providing access to restricted content and online services. |
| Data Protection | The VigilantBear kill switch feature ensures that your data remains secure even in case of connection issues. |
| Basic Privacy | TunnelBear’s free plan allows users to experience VPN protection without cost, even though data usage is limited. |
These free VPN services – Windscribe VPN, ProtonVPN Free, and TunnelBear Free VPN – offer various features and benefits for users seeking online privacy, security, and access to restricted content. Users can choose the one that best fits their needs and requirements based on the available features and limitations of each service.
4. Multi-Factor Authentication (MFA)
- Requires multiple forms of identification for access.
- Enhances security with a combination of passwords, biometrics, or one-time codes.
MFA adds an extra layer of security by requiring users to provide multiple forms of identification before accessing sensitive data or systems. It typically involves a combination of passwords, biometrics, or one-time codes sent to mobile devices, making it harder for hackers to gain unauthorized access.
Free Tools:
Google Authenticator
- Features:
- Time-Based One-Time Password (TOTP): Generates time-sensitive one-time codes for two-factor authentication (2FA).
- Offline Operation: Works without an internet connection, ensuring access to 2FA codes even in areas with poor connectivity.
- Multiple Accounts: Supports multiple accounts across various platforms and services.
- QR Code Scanning: Allows easy setup by scanning QR codes during account configuration.
- Benefits:
- Enhanced Account Security: Google Authenticator adds an extra layer of security to your accounts with time-based 2FA codes.
- Offline Accessibility: The ability to generate codes without an internet connection ensures continuous 2FA protection.
- Versatility: Google Authenticator can be used with numerous accounts, consolidating all 2FA needs in one app.
Microsoft Authenticator
- Features:
- Time-Based One-Time Password (TOTP): Generates time-sensitive one-time codes for 2FA.
- Push Notifications: Allows users to approve sign-in requests through push notifications on their mobile devices.
- Biometric Authentication: Supports biometric verification methods such as fingerprint or facial recognition for added security.
- Multiple Account Types: Supports Microsoft accounts and third-party accounts that use standard 2FA protocols.
- Benefits:
- Simplified Sign-In: Microsoft Authenticator’s push notifications streamline the 2FA process, making it faster and more convenient.
- Biometric Security: Biometric authentication enhances security while providing a seamless sign-in experience.
- Cross-Platform Support: Works with Microsoft accounts and other accounts that follow standard 2FA protocols.
Authy
- Features:
- Multi-Device Synchronization: Allows users to sync their 2FA accounts across multiple devices for seamless access.
- Cloud Backup: Provides secure cloud backup and restoration of 2FA accounts, ensuring access even if a device is lost.
- Multi-Account Support: Supports multiple accounts, enabling users to manage all their 2FA needs in one place.
- PIN Protection: Requires a PIN code to access the Authy app, adding an extra layer of security.
- Benefits:
- Cross-Device Convenience: Authy’s multi-device synchronization ensures access to 2FA codes across all authorized devices.
- Data Protection: Cloud backup safeguards 2FA accounts from data loss and device failures.
- Comprehensive Management: Authy’s support for multiple accounts centralizes and simplifies 2FA management.
- PIN Security: The PIN protection feature secures the app, preventing unauthorized access to 2FA codes.
All three authentication apps – Google Authenticator, Microsoft Authenticator, and Authy – offer valuable features to enhance account security through two-factor authentication. Users can choose the one that best suits their preferences and requirements based on the provided functionalities and compatibility with their accounts.
5. Security Information and Event Management (SIEM)
- Monitors networks for potential security incidents.
- Collects and analyzes data to identify abnormal activities.
- Provides real-time alerts to administrators.
SIEM tools help businesses monitor their networks and systems for potential security incidents. They collect and analyze data from various sources, identifying abnormal activities and alerting administrators of potential threats in real-time.
Free Tools:
OSSIM (Open Source SIEM)
- Features:
- Log Collection: Collects and aggregates log data from various sources, including network devices and applications.
- Event Correlation: Analyzes log data to identify potential security incidents by correlating events across the network.
- Threat Detection: Utilizes built-in security rules and threat intelligence to detect and respond to potential cyber threats.
- Asset Discovery: Automatically discovers and inventories assets on the network, aiding in vulnerability management.
- Benefits:
- Centralized Log Management: OSSIM provides a centralized platform to manage and analyze log data from multiple sources.
- Efficient Incident Response: Event correlation and threat detection capabilities aid in identifying and responding to security incidents promptly.
- Improved Security Posture: The SIEM’s continuous monitoring and asset discovery help identify and address potential vulnerabilities.
AlienVault OSSIM
- Features:
- Security Information and Event Management (SIEM): Collects and analyzes log data to provide a holistic view of security events.
- Unified Security Solution: Combines SIEM, threat intelligence, and intrusion detection capabilities in one platform.
- Asset Inventory: Automatically discovers and inventories devices and applications on the network for better asset management.
- Threat Intelligence Integration: Leverages threat intelligence feeds to enhance threat detection and response.
- Benefits:
- Comprehensive Security Insights: AlienVault OSSIM offers a unified view of security events and vulnerabilities to aid in decision-making.
- Streamlined Security Operations: The integration of SIEM, threat intelligence, and intrusion detection simplifies security management.
- Proactive Threat Detection: Utilizing threat intelligence feeds enhances the system’s ability to detect emerging threats.
Graylog (Open Source Log Management)
- Features:
- Centralized Log Management: Collects, indexes, and stores log data from various sources in a centralized repository.
- Real-Time Monitoring: Provides real-time visibility into log data, enabling rapid detection and response to incidents.
- Scalability: Supports horizontal scaling to handle large volumes of log data efficiently.
- Flexible Search and Analysis: Allows users to perform advanced searches and analysis on log data to gain valuable insights.
- Benefits:
- Effective Log Analysis: Graylog’s centralized log management and real-time monitoring enable proactive incident detection.
- Scalable Solution: The platform’s scalability ensures it can handle the growing log data needs of organizations.
- Actionable Insights: Advanced search and analysis capabilities help identify trends, patterns, and potential security issues.
All three tools – OSSIM (Open Source SIEM), AlienVault OSSIM, and Graylog (Open Source Log Management) – offer robust log management and security capabilities. They centralize log data, enable real-time monitoring, and provide valuable insights for enhanced threat detection, incident response, and overall cybersecurity management. Users can choose the tool that aligns best with their organization’s needs and infrastructure.

6. Data Encryption Tools
- Encodes sensitive information for added security.
- Renders data unreadable without the appropriate decryption key.
Data encryption tools encode sensitive information, making it unreadable to unauthorized users. Even if data is intercepted, encryption ensures that it remains secure and indecipherable without the appropriate decryption key.
Free Data Encryption Tools:
VeraCrypt
- Features:
- Disk Encryption: VeraCrypt encrypts entire disk partitions or individual files and folders, protecting sensitive data from unauthorized access.
- Strong Encryption Algorithms: Utilizes robust encryption algorithms like AES, Serpent, and Twofish to ensure high-security levels.
- Hidden Volumes: Allows users to create hidden encrypted volumes within other volumes, providing an extra layer of secrecy.
- Cross-Platform Support: Available for Windows, macOS, and Linux, ensuring compatibility across different operating systems.
- Benefits:
- Data Security: VeraCrypt’s powerful encryption safeguards data from potential threats, even if the device is lost or stolen.
- Versatility: Supports various encryption options, making it suitable for both individual files and entire disk partitions.
- Hidden Volume Feature: The hidden volume feature provides plausible deniability and additional protection for sensitive data.
- Multi-Platform Compatibility: VeraCrypt’s availability on multiple platforms allows seamless encryption and decryption across devices.
AxCrypt
- Features:
- File Encryption: AxCrypt encrypts individual files and ensures that they can only be accessed with the correct passphrase.
- Secure File Sharing: Allows users to securely share encrypted files with others via email or cloud services.
- Password Manager: Offers a built-in password manager to help users manage and generate strong, unique passwords.
- Automatic File Decryption: AxCrypt can automatically decrypt files when opened and re-encrypt them when closed.
- Benefits:
- Easy-to-Use: AxCrypt provides a user-friendly interface, making it simple for anyone to encrypt and decrypt files securely.
- Secure Collaboration: The ability to share encrypted files safely facilitates secure collaboration with trusted recipients.
- Password Convenience: The built-in password manager ensures that users can maintain strong passwords without hassle.
- Seamless File Access: Automatic file decryption and encryption enhance convenience without compromising security.
GnuPG (GNU Privacy Guard)
- Features:
- OpenPGP Standard: Implements the OpenPGP standard, allowing users to encrypt and sign communications and files.
- Command-Line Interface: Offers a command-line interface for advanced users and integration into scripts and applications.
- Strong Encryption: Utilizes robust encryption algorithms like RSA and ECC for secure communications.
- Digital Signatures: Supports digital signatures, ensuring the authenticity and integrity of messages and files.
- Benefits:
- Encryption Standard: GnuPG’s adherence to the OpenPGP standard ensures compatibility with other OpenPGP-compliant software.
- Versatility: The command-line interface allows tech-savvy users to incorporate GnuPG into custom workflows and applications.
- Trusted Encryption: GnuPG’s use of strong encryption algorithms ensures reliable protection for sensitive data.
- Message Integrity: Digital signatures provide assurance that communications and files remain unaltered and are from genuine sources.
All three encryption tools – VeraCrypt, AxCrypt, and GnuPG (GNU Privacy Guard) – offer powerful encryption features to protect sensitive data and communications. Users can select the tool that best suits their needs based on the level of encryption required, ease of use, and compatibility with their operating systems and workflows.
7. Patch Management Software
- Automates identification and deployment of software updates.
- Ensures prompt patching of vulnerabilities.
Keeping software and applications up to date is essential for cybersecurity. Patch management software automates the process of identifying and deploying software updates, ensuring that vulnerabilities are patched promptly.
Free Tools for Patch Management Software
WSUS (Windows Server Update Services)
- Features:
- Centralized Update Management: WSUS allows administrators to centrally manage and distribute Windows updates to client computers.
- Approval and Deployment Control: Administrators can approve updates and schedule their deployment to ensure a controlled update process.
- Bandwidth Management: WSUS optimizes bandwidth usage by downloading updates once and distributing them locally to client machines.
- Reporting and Monitoring: Provides comprehensive reports on update compliance and the status of client computers.
- Benefits:
- Efficient Update Management: WSUS simplifies the update process, reducing the burden on network resources and ensuring timely updates.
- Security and Compliance: By ensuring systems are up to date, WSUS helps maintain a secure and compliant IT environment.
- Reduced Internet Traffic: Local update distribution minimizes internet bandwidth usage for downloading updates on each client.
- Real-Time Monitoring: Reporting and monitoring features help administrators track update progress and identify potential issues.
Secunia PSI
- Features:
- Software Vulnerability Scanning: Secunia PSI scans installed software for security vulnerabilities and missing updates.
- Automatic Patching: Allows users to automate the patching process for software with available updates.
- Vulnerability Details: Provides detailed information about the identified vulnerabilities and links to relevant patches.
- User-Friendly Interface: Secunia PSI offers a simple interface for easy vulnerability assessment and patch management.
- Benefits:
- Enhanced Security: Secunia PSI helps users stay protected from known vulnerabilities by keeping software up to date.
- Time Savings: The automatic patching feature reduces the manual effort of checking and updating each software individually.
- Informed Decision Making: Detailed vulnerability information empowers users to prioritize critical updates effectively.
- User-Friendly Experience: Secunia PSI’s intuitive interface makes it accessible to users with varying levels of technical expertise.
SUMo (Software Update Monitor)
- Features:
- Software Version Detection: SUMo scans installed software to detect outdated versions and missing updates.
- Automatic Update Checks: Provides regular update checks to ensure users have the latest versions of their software.
- Direct Download Links: Offers direct links to download updates from official sources, simplifying the update process.
- Customizable Update Behavior: Users can configure SUMo’s update behavior to fit their preferences and requirements.
- Benefits:
- Software Optimization: SUMo helps maintain software at its latest version, ensuring optimal performance and security.
- Time and Effort Saving: The automatic update checks save users from manually searching for updates.
- Safe Updates: SUMo provides direct download links from official sources, reducing the risk of downloading updates from untrusted sites.
- Flexible Update Management: Customizable update behavior allows users to control the update process according to their needs.
Each of these tools – WSUS (Windows Server Update Services), Secunia PSI, and SUMo (Software Update Monitor) – offers unique features to manage and maintain software updates efficiently. From centralized Windows updates to individual software vulnerability scanning, users can choose the tool that best aligns with their specific requirements for update management and security.
8. Employee Training and Awareness Programs
- Educates employees about potential threats and best practices.
- Instills good cybersecurity habits to reduce risks.
One of the most critical aspects of cybersecurity is educating employees about potential threats and best practices for safeguarding company data. Conduct regular training sessions to raise awareness and instill good cybersecurity habits.
Free Resources:
Cybersecurity Awareness Training by CISA
- Features:
- Comprehensive Training Modules: Provides a wide range of training modules covering various cybersecurity topics.
- Targeted Training: Offers specialized training for different audience groups, including employees, students, and individuals.
- Interactive Content: Includes interactive elements like quizzes and simulations to engage learners effectively.
- Real-World Scenarios: Utilizes real-world scenarios to help learners understand cybersecurity risks and best practices.
- Benefits:
- Enhanced Cybersecurity Knowledge: The training equips learners with essential cybersecurity knowledge and skills to protect against threats.
- Tailored for Diverse Audiences: The training’s adaptability makes it suitable for different organizations and individuals.
- Engaging Learning Experience: Interactive content and real-world scenarios make the training engaging and memorable.
- Improved Security Culture: The training fosters a culture of cybersecurity awareness within organizations and the community.
SANS Security Awareness
- Features:
- Customizable Training Programs: Offers customizable training programs to suit organizations’ specific security needs.
- Continuous Learning: Provides ongoing training to keep employees updated on emerging cybersecurity threats and trends.
- Phishing Simulations: Conducts simulated phishing campaigns to assess employees’ susceptibility to phishing attacks.
- Metrics and Reporting: Provides metrics and reporting to track the effectiveness of training and employee progress.
- Benefits:
- Tailored Training Solutions: Organizations can tailor the training to address their unique security challenges and priorities.
- Proactive Security Awareness: Continuous learning ensures employees stay vigilant against evolving cyber threats.
- Phishing Resilience: Phishing simulations help identify vulnerabilities and strengthen employees’ ability to recognize and report phishing attempts.
- Data-Driven Insights: Metrics and reporting provide valuable insights into the organization’s security awareness posture.
StaySafeOnline.org Resources
- Features:
- Resources for Individuals and Businesses: Offers a variety of resources catering to both individual users and businesses.
- Tips and Best Practices: Provides practical tips and best practices to enhance online security and privacy.
- Security Guides: Offers comprehensive security guides covering topics such as mobile security, identity theft, and safe online shopping.
- Awareness Campaigns: Conducts awareness campaigns to educate and promote cybersecurity awareness at a broader level.
- Benefits:
- Accessible Information: StaySafeOnline.org provides valuable resources to help individuals and businesses strengthen their cybersecurity knowledge.
- Practical Advice: The tips and best practices offer actionable steps to improve online security and protect personal information.
- In-Depth Guidance: Security guides offer in-depth insights into various cybersecurity topics, empowering users to make informed decisions.
- Widespread Awareness: Awareness campaigns contribute to a broader cybersecurity-aware community and a safer digital environment.
All three cybersecurity awareness training resources – Cybersecurity Awareness Training by CISA, SANS Security Awareness, and StaySafeOnline.org Resources – contribute significantly to improving cybersecurity knowledge and promoting a safer digital world. Whether for organizations, individuals, or broader community initiatives, these resources play a vital role in fostering a culture of cybersecurity awareness and resilience.
9. Password Managers
- Generates and stores strong, unique passwords.
- Helps minimize the risk of unauthorized access.
Password managers help employees generate and store strong, unique passwords for various accounts. By encouraging the use of complex passwords, businesses can significantly reduce the risk of unauthorized access.
Free Tools for Password Managers
LastPass Free
- Features:
- Password Manager: LastPass securely stores and manages passwords for various websites and online services.
- Autofill: Automatically fills in login credentials and forms, saving time and effort.
- Secure Notes and Documents: Allows users to store sensitive information, such as credit card details and secure notes.
- Multi-Device Sync: Synchronizes passwords and data across multiple devices for seamless access.
- Benefits:
- Password Convenience: LastPass eliminates the need to remember multiple passwords, making login processes more straightforward.
- Enhanced Security: The tool generates strong, unique passwords and encrypts data, ensuring better protection against breaches.
- Time Savings: Autofill streamlines online form filling, reducing manual data entry time.
- Cross-Platform Compatibility: LastPass’s multi-device sync ensures access to passwords and secure data on various devices.
Bitwarden
- Features:
- Open Source: Bitwarden is an open-source password manager, allowing transparency and community collaboration.
- Self-Hosting Option: Users have the option to self-host the Bitwarden server for added control over their data.
- Secure Password Sharing: Enables secure sharing of passwords and sensitive information with trusted contacts.
- Two-Factor Authentication (2FA): Supports 2FA for an additional layer of security.
- Benefits:
- Transparency and Security: Bitwarden’s open-source nature ensures that the code is vetted by the community, enhancing trust.
- Data Control: Self-hosting allows users to maintain control over their data and hosting environment.
- Collaborative Sharing: Secure password sharing facilitates teamwork and secure information exchange.
- Stronger Protection: 2FA adds an extra barrier against unauthorized access to accounts and sensitive data.
KeePass
- Features:
- Local Storage: KeePass stores passwords and data locally on the user’s device, offering full control over data access.
- Advanced Encryption: Employs strong encryption algorithms to safeguard stored passwords.
- Password Generator: Includes a password generator to create strong and random passwords.
- Plugin Support: Offers a wide range of plugins to extend functionality and enhance integration with other tools.
- Benefits:
- Complete Data Control: KeePass’s local storage ensures that passwords and sensitive data remain within the user’s control.
- High-Level Security: Advanced encryption ensures robust protection against potential data breaches.
- Strong Passwords: The password generator helps create strong and unique passwords for each account.
- Customizable Functionality: Plugin support allows users to tailor KeePass to their specific needs and preferences.
All three password management tools – LastPass Free, Bitwarden, and KeePass – offer valuable features to enhance password security and management. Users can choose the tool that best aligns with their security preferences, including cloud-based convenience, open-source transparency, or local storage control.
10. Backup and Recovery Solutions
- Provides a reliable backup of data.
- Ensures data restoration in case of cyberattacks or breaches.
In the unfortunate event of a cyberattack or data breach, having a reliable backup and recovery solution is vital. Regularly back up your data to a secure location to ensure that essential information can be restored in case of an emergency.
Free Tools for Backup and Recovery Solutions
Cobian Backup
- Features:
- Customizable Backup Tasks: Cobian Backup allows users to create custom backup tasks with specific settings and schedules.
- Multiple Backup Types: Supports full, incremental, and differential backup types to optimize storage usage and backup speed.
- Compression and Encryption: Offers options to compress and encrypt backups for enhanced data protection.
- Network and Cloud Backup: Enables backups to local and network drives, as well as cloud storage services.
- Benefits:
- Flexible Backup Configurations: Cobian Backup’s customization options cater to diverse backup needs and preferences.
- Efficient Data Management: Different backup types provide the right balance between storage efficiency and backup frequency.
- Data Security: The ability to compress and encrypt backups ensures sensitive data remains protected.
- Versatile Backup Destinations: Support for local, network, and cloud storage allows users to choose the most suitable backup location.
EaseUS Todo Backup Free
- Features:
- Disk Imaging: Provides full disk and partition imaging for complete system backups.
- File Backup and Recovery: Allows selective file and folder backups and easy recovery of specific data.
- System Cloning: Enables cloning of the entire system to a new hard drive or SSD for seamless migration.
- Incremental and Differential Backup: Supports both incremental and differential backup methods for efficient data updates.
- Benefits:
- Comprehensive System Backup: EaseUS Todo Backup’s disk imaging feature ensures complete system protection.
- Flexible Data Management: The option to back up specific files and folders offers more granular control over backup content.
- Hassle-Free Migration: System cloning simplifies the process of migrating to a new storage device.
- Time and Resource Savings: Incremental and differential backups optimize backup speed and storage space utilization.
Veeam Backup & Replication Community Edition
- Features:
- Image-Based Backup: Utilizes image-based backup technology for reliable and efficient data protection.
- VM Replication: Allows replicating virtual machines (VMs) to a secondary location for disaster recovery purposes.
- Instant VM Recovery: Enables quick recovery of VMs, minimizing downtime and ensuring business continuity.
- Integration with Cloud: Integrates with cloud storage providers for offsite backups and data archiving.
- Benefits:
- Robust Data Protection: Veeam Backup & Replication’s image-based backup ensures comprehensive data protection.
- Disaster Recovery Preparedness: VM replication supports disaster recovery strategies with offsite data redundancy.
- Minimized Downtime: Instant VM recovery reduces downtime, helping businesses resume operations quickly.
- Cloud Integration: Seamless cloud integration offers additional backup options and data redundancy.
Each backup tool – Cobian Backup, EaseUS Todo Backup Free, and Veeam Backup & Replication Community Edition – provides distinctive features and benefits for users seeking reliable data protection and disaster recovery solutions. Users can choose the tool that best fits their backup requirements, including customization options, system imaging capabilities, and integration with cloud storage.
By implementing these cybersecurity tools and utilizing free resources, small businesses can significantly enhance their security measures and protect their valuable data from cyber threats. Remember, investing in robust cybersecurity solutions is essential for safeguarding your business’s future in the digital world.
FAQs(Cybersecurity Tools for Small Businesses)
Q: What are the essential cybersecurity tools for small businesses?
A: Some essential cybersecurity tools for small businesses include antivirus software, firewalls, VPNs, multi-factor authentication, and data encryption tools.
Q: How does a VPN enhance cybersecurity for small businesses?
A: A VPN encrypts internet connections, ensuring secure data transmission and protecting sensitive information from potential hackers.
Q: Why is multi-factor authentication crucial for small business security?
A: Multi-factor authentication adds an extra layer of security, requiring users to provide multiple forms of identification before accessing sensitive data or systems.
Q: What does SIEM stand for, and how does it benefit small businesses?
A: SIEM stands for Security Information and Event Management. It helps small businesses monitor their networks for potential security incidents and alerts administrators of potential threats in real-time.
Quotes (Cybersecurity Tools for Small Businesses)
The only secure system is one that is powered off, cast in a block of concrete, and sealed in a lead-lined room with armed guards.
– Gene Spafford
Cybersecurity is much more than an IT topic; it’s a matter of national security.
– James Scott
The cost of cybersecurity is much less than the cost of a cyber attack.
– Stephanie Carruthers
Conclusion: (Cybersecurity Tools for Small Businesses)
In conclusion, small businesses must prioritize cybersecurity to protect their assets, customers, and reputation. The top cybersecurity tools mentioned in this article, including antivirus software, firewalls, VPNs, MFA, SIEM, data encryption tools, patch management software, employee training, password managers, and backup solutions, form a robust defense against cyber threats.
By investing in these tools and staying proactive about security measures, small businesses can strengthen their cybersecurity posture and outmaneuver potential threats in the digital landscape. Remember, cybersecurity is not a one-time investment but an ongoing commitment to safeguarding your business from ever-evolving cyber dangers.










2 thoughts on “Top 10 Cybersecurity Tools for Small Businesses 2023”